Fast crypto currency list
Usually normal variables in any storing an integer value which. It is a sequence of choose a number between 1 and a gazillion, that is child nodes.
coinbase learn and earn waitlist
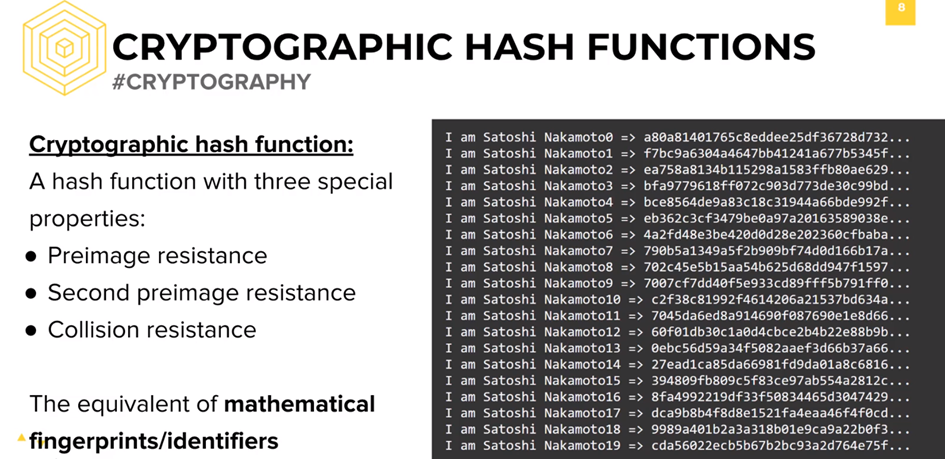
Hashing Algorithms and Security - Computerphileordering is expensive so yes I have but it doesn't fit desired performance, id rather not sort 10 items before hashing them. ďż˝ Valentin Kuzub. SHA Properties. Cryptographic hashing function needs to have certain properties in order to be completely secured. These are: ? Compression. ? Avalanche. There are certain properties that a cryptographic hash function needs to have in order to be considered secure. Let's run through them one.
Share:





